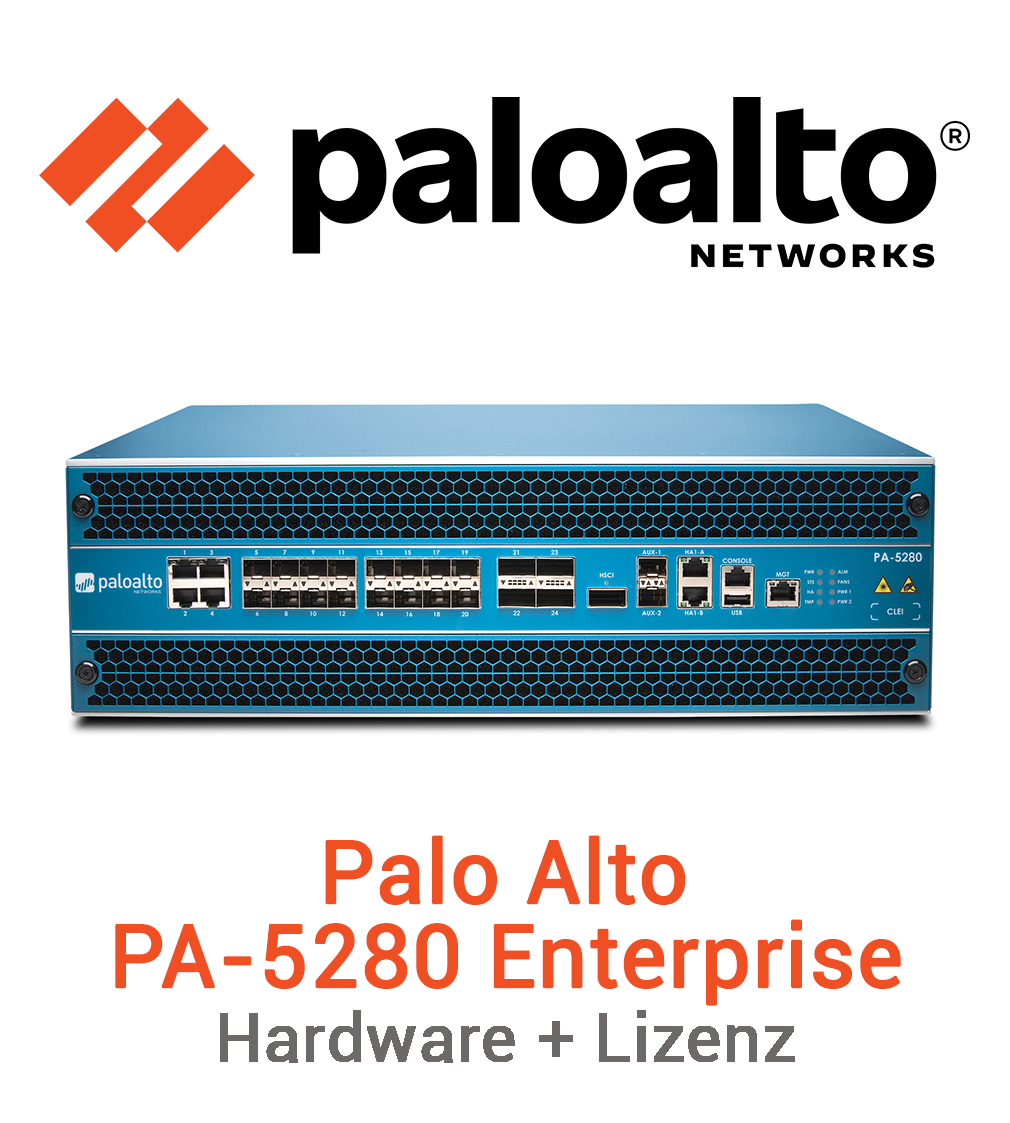
Palo Alto PA-5280
Die PA-5400 Series nutzt das Betriebssystem PAN-OS®, wie alle NGFWs von Palo Alto Networks. PAN-OS klassifiziert nativ den gesamten Netzwerkverkehr (einschließlich aller Anwendungsdaten, Bedrohungen und legitimen Inhalte) und ordnet die einzelnen Pakete anschließend unabhängig vom Standort oder Gerätetyp einem Benutzer zu. In Abhängigkeit von den Anwendungen, Inhalten und Benutzern (also den Faktoren, die für Ihr Geschäft relevant sind) wird dann entschieden, welche Sicherheitsrichtlinien anzuwenden sind. Das stärkt die Sicherheit und beschleunigt effektive Reaktionen auf Sicherheitsvorfälle.
The increasing number of well-disguised and automated attacks has become one of the biggest concerns for network security teams. Modern hackers have access to sophisticated tools, use criminally targeted as-a-service models, and abuse versions of common red-team solutions - causing more damage faster with attacks that are designed for the long term and carefully disguised. Cyberattacks that leverage the easily accessible and highly customizable Cobalt Strike penetration testing tool have increased 73 percent year-over-year. And that's just the beginning of a new wave of well-disguised attacks that organizations face today.1 Encryption techniques are also being used by malicious actors to bypass traditional security measures. Studies show that malware is now primarily introduced over encrypted connections.2 Network security must keep pace with these developments to stop well-disguised and unknown threats.
The increasing number of well-disguised and automated attacks has become one of the biggest concerns for network security teams. Modern hackers have access to sophisticated tools, use criminally targeted as-a-service models, and abuse versions of common red-team solutions - causing more damage faster with attacks that are designed for the long term and carefully disguised. Cyberattacks that leverage the easily accessible and highly customizable Cobalt Strike penetration testing tool have increased 73 percent year-over-year. And that's just the beginning of a new wave of well-disguised attacks that organizations face today.1 Encryption techniques are also being used by malicious actors to bypass traditional security measures. Studies show that malware is now primarily introduced over encrypted connections.2 Network security must keep pace with these developments to stop well-disguised and unknown threats.
Palo Alto Networks PA-5200 Series ML-Powered NGFWs—the PA-5280, PA-5260, PA-5250, and PA-5220—are ideal for high-speed data center, internet gateway, and service provider deployments. The PA-5200 Series delivers up to 64 Gbps of throughput, using dedicated processing and memory, for the key functional areas of networking, security, threat prevention, and management.
Highlights:
- World’s first ML-Powered NGFW
- Eleven-time Leader in the Gartner Magic Quadrant for Network Firewalls
- Leader in The Forrester Wave: Enterprise Firewalls, Q4 2022
- Delivers 5G-Native Security built to safeguard service provider and enterprise 5G transformation and multi-access edge computing (MEC)
- Extends visibility and security to all devices, including unmanaged IoT devices, without the need to deploy additional sensors
- Supports high availability with active/active and active/passive modes
- Delivers predictable performance with security services
- Supports centralized administration with Panorama network security management
- Maximizes security investments and prevents business disruptions with Strata ™ Cloud Manager
The world’s first ML-Powered Next-Generation Firewall (NGFW) enables you to prevent unknown threats, see and secure everything—including the internet of things (IoT)—and reduce errors with automatic policy recommendations. The controlling element of the PA-5200 Series is PAN-OS ® , the same software that runs all Palo Alto Networks NGFWs. PAN-OS natively classifies all traffic, inclusive of applications, threats, and content, and then ties that traffic to the user regardless of location or device type. The application, content, and user—in other words, the elements that run your business— then serve as the basis of your security policies, resulting in improved security posture and reduced incident response time.