
What are actually... UTM Firewalls?
On our own behalf
Many manufacturers today advertise with the term UTM firewall. But what is behind the term UTM firewall?
First of all, let's take a look at the narrow but, for the first overview, sufficient definition by Wikipedia for an initial overview:
Unified Threat Management
Unified Threat Management (UTM) is a term coined by Charles Kolodgy of International Data Corporation (IDC) in 2004. In network security systems, a distinction is made between Specialised Security Appliances (SSA), which are designed for a specific task, and Unified Threat Management Appliances (UTMA), which combine different security tasks on one platform. The goal of the UTM is to achieve security for the entire network at a central point.
The prerequisite for the designation "Unified Threat Management System" is a functional combination of:
- Internet gateway
- Firewall
- Virtual Private Network (VPN) Gateway
- Virus protection
- Intrusion detection system
- Content Filter
- Spam Protection
- Surf Protection
- Authentication
- Quality of Service (QoS)
- Reporting
UTM firewalls in comparison
We can thus already state that there is a uniform standard for the term Unified Threat Management (UTM). The different firewall manufacturers therefore have the same basic functions as soon as the slogan UTM appears on the product. Nevertheless, there are differences that need to be taken into account.
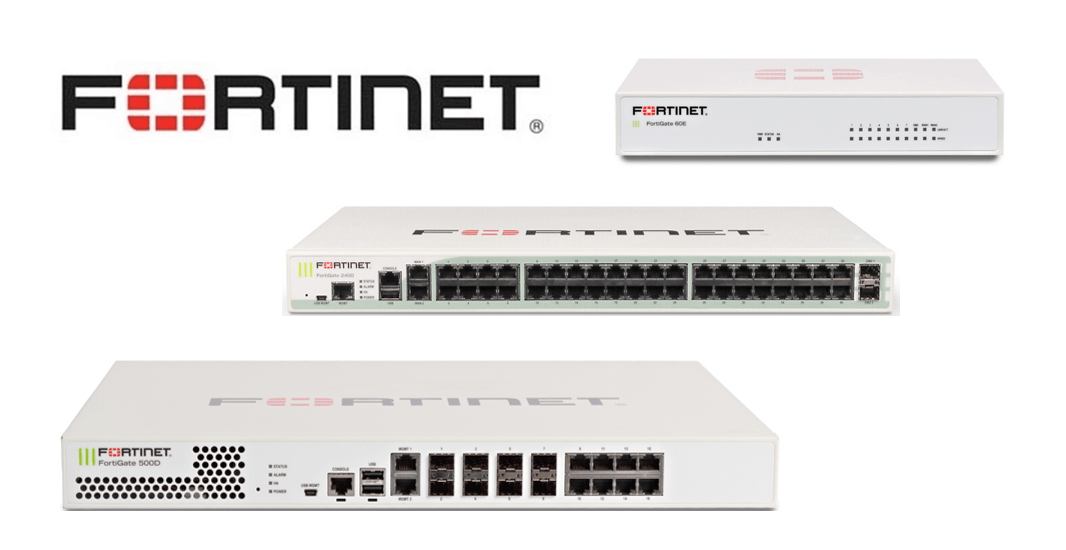
Fortinet UTM Firewalls
If you are looking for a solution that can be "tailor-made" for your company, then Fortinet is the right choice. Not only in terms of pure data throughput, but also in terms of connections. Most models have SFP ports where both copper and fibre optic transceivers can be connected.
Fortinet also offers modular expandability for your security solution.
If you need stronger protection for email traffic, FortiMail is available as a VM or hardware appliance. Are you looking for a sandbox solution where the data does not leave your network? Then a FortiSandbox is the solution for you. Do you want to operate a WLAN in your company that provides both a fast and secure wireless network? Fortinet has a wide range of access points that can be managed via a FortiGate, the online platform Forticloud or even via dedicated WLAN controllers. For direct protection and compliance monitoring, Fortinet offers FortiClient, which is more than just anti-virus protection. It also actively searches for vulnerabilities caused by outdated software and offers a VPN client. The administrator also has the option of monitoring the status of the clients via a central administration point and rolling out VPN configurations without having to install them manually on the individual clients.
Thanks to the Fortinet Security Fabric, the devices can also be networked with each other without great effort and information can be exchanged quickly in the event of a security incident and appropriate countermeasures can be taken. For example, by isolating infected endpoints.
Sophos UTM Firewalls
Sophos follows a different path than Fortinet. Here, the firewalls are all-rounders. For example, in email and anti-spam protection, Sophos firewalls offer more features than a Fortigate firewall. On the other hand, Sophos lacks the modularity that characterises Fortinet. When expanding ports, Sophos relies on so-called Flexi Port Modules. Here, entire port groups are offered as a module. These can be installed in the device with very little effort.
Another strong point of Sophos is endpoint protection. Sophos offers a strong selection of protection and encryption solutions, both for desktop PCs, servers and mobile devices based on iOS and Android. A firewall is optional here, as Sophos offers the Central Cloud Platform as a management interface.
Sophos offers so-called REDs, Remote Ethernet Devices, for the connection of remote offices. These can be sent directly to a remote office and automatically provided with a configuration that has been stored by an administrator on the Sophos platform. This makes it both easy and very cost-effective to securely connect remote offices to the central office.
For the provision of a WLAN, Sophos offers a selection of access points that can be managed either via Sophos Central or a Sophos firewall.
Just like Fortinet, Sophos offers a network of Sophos products with Synchronised Security. As with Fortinet, this allows compliance rules to be enforced as well as isolating the device in question in the event of an incident.
Stormshield UTM Firewalls
Stormshield is ideal for companies that have to deal with sensitive information and require absolute transparency of the devices in use. Stormshield has disclosed the complete source code of its software to independent institutes in Europe in order to obtain the coveted EU/EAA and NATO Restricted classification.
Stormshield is a European company and a 100% subsidiary of Airbus CyberSecurity.
In addition to UTM firewalls, Stormshield also offers hardening solutions. Thanks to these, you can control very granularly what the employees in your company can do on the individual systems. You can even go so far as to allow only very specific USB sticks. In addition, you are able to determine which systems software is allowed to connect to and can thus directly prevent unauthorised access to other systems. This also works for offline systems, which is a great advantage in isolated environments.
As additional virus protection for end devices, Stormshield offers BreachFighter. Based on the Kaspersky Engine, data is analysed in a sandbox in European data centres in accordance with the DSGVO and the result is made available to all users of BreachFighter. By sharing threat information, you can benefit from others and actively counteract the spread of malware.
Conclusion
All manufacturers have their raison d'être and score in different areas. If you are not sure which is the right UTM firewall for you, simply contact our experts.
Marcel Zimmer is the Technical Managing Director of EnBITCon. During his time in the German Armed Forces, the trained IT developer was able to gain numerous project experiences. His interest in IT security was significantly awakened by his service in command support. Even after his service, he is an active reservist in the Bundeswehr.
His first firewall was a Sophos UTM 120, which he had to set up for a customer project. Since then, his interest in IT security has grown steadily. In the course of time, various security and infrastructure topics have come into his focus. His most interesting projects included, for example, WLAN coverage in an explosion-proof area, as well as a multi-site WLAN solution for a large














